Your SciOly Coach
How to Solve a Nihilist Cryptanalysis Cipher! (Digital)
5 months ago - 36:53

Kawaiicon NZ
Peter Gutmann - Why Quantum Cryptanalysis is Bollocks
4 months ago - 31:17

Proof of Concept
Cryptanalysis of Vigenere cipher: not just how, but why it works
5 years ago - 15:33

Cryptography for Everybody
Hello and welcome to my cryptology channel! I am Nils, a cryptology maniac and specialist. Currently, I lead the development of ...
@CryptographyForEverybody subscribers

Keith Simonsen
Differential Cryptanalysis for Dummies - Layerone 2013
12 years ago - 38:49

Fireship
7 Cryptography Concepts EVERY Developer Should Know
4 years ago - 11:55

CrashCourse
Cryptography: Crash Course Computer Science #33
8 years ago - 12:33

Eye on Tech
What is Post-Quantum Cryptography?
9 months ago - 5:11

SciShow
The Science of Codes: An Intro to Cryptography
10 years ago - 8:21

Veritasium
What makes quantum computers SO powerful?
3 years ago - 24:29

Chalk Talk
Lattice-based cryptography: The tricky math of dots
3 years ago - 8:39

LEMMiNO
The Unbreakable Kryptos Code
2 years ago - 47:01

Jens Puhle
Cryptanalysis: Breaking a Vigenère ciphertext with Kasiski's test
2 years ago - 8:47

Maria Eichlseder
Cryptanalysis - L6 Differential Cryptanalysis
Streamed 5 years ago - 2:34:48

The Boring Scientist
The Complete History of Cryptography: The Evolution of Secret Communication | Science for Sleep
6 months ago - 1:42:46

Practical Networking
Encryption - Symmetric Encryption vs Asymmetric Encryption - Cryptography - Practical TLS
4 years ago - 13:58

Pico Cetef
Cryptography 101 - The Basics
13 years ago - 8:57

What is cybersecurity?
What is the difference between cryptography, cryptanalysis and cryptology?
2 years ago - 1:14

The Security Buddy
Cryptography vs. Cryptology vs. Cryptanalysis - What is the difference?
4 years ago - 2:42

Prabh Nair
Cryptography Fundamentals 2022
4 years ago - 32:46

Computerphile
Post Quantum Cryptography - Computerphile
1 month ago - 13:27

Computerphile
Public Key Cryptography - Computerphile
11 years ago - 6:20

Zach Star
The Mathematics of Cryptography
7 years ago - 13:03

Nerd's lesson
Cryptography Full Course Part 1
5 years ago - 8:17:38

Maria Eichlseder
Cryptanalysis - L8 Linear Cryptanalysis
Streamed 5 years ago - 2:00:52

Be The Best
CSS #9 Cryptanalytic attacks|Ciphertext only|Known Plaintext|Chosen Plaintext|Chosen Ciphertext|BTB
3 years ago - 8:37

Professor Messer
Cryptography Concepts - SY0-601 CompTIA Security+ : 2.8
5 years ago - 5:31

Simplilearn
Cryptography Full Course | Cryptography And Network Security | Cryptography | Simplilearn
Streamed 4 years ago - 2:15:01

Maria Eichlseder
@meichlseder subscribers

The Salmon Runs
Linear vs Differential Cryptanalysis - 2025 Comparison
8 months ago - 2:26

Introduction to Cryptography by Christof Paar
The 24 lectures give a comprehensive introduction to modern applied crypto. Only high school math is required to follow the ...
@introductiontocryptography4223 subscribers

BrevityBrains
Modern Applications of Cryptanalysis
2 years ago - 4:13

Veritasium
What makes quantum computers SO powerful?
3 years ago - 24:29

Jignesh Patel
Unit 2 2 Cryptanalysis The Science of Code Breaking
5 months ago - 2:59

Future Histories
Cracking the Codes: How WWII Cryptanalysis Shaped History and Technology
1 year ago - 1:03

The Cur[AI]tor
The Art of Ancient Cryptography Explained #AncientCryptography #History #Cipher
1 year ago - 0:52

Cihangir Tezcan
Applied Cryptology 5.2: Differential Cryptanalysis
5 years ago - 19:51

Amit Kukreja
PPI INFLATION DATA, JENSEN HEADS TO CHINA, NEBIUS CRUSHES EARNINGS, THE SEMIS ARE BACK | MARKET OPEN
-

Cyber Pioneers
Cryptanalysis Cyber Attacks Explained
4 years ago - 2:59

IACR
Differential Cryptanalysis in the Fixed-Key Model
3 years ago - 5:05

Cryptography for Everybody
Basics of Cryptology – Part 10 (Modern Cryptanalysis of Classical Ciphers – Genetic Algorithm)
5 years ago - 16:16

Cryptography 101
Lectures by Alfred Menezes on applied cryptography and related areas.
@cryptography101-alfred subscribers

InfoSec Guardians
🔍 Cryptanalysis in 60 Seconds! 🕵️♂️ #cryptography #infosec #CyberDefense #cissp #cism #ccsp #cisa
2 years ago - 0:59

codeworkbench
Fall Asleep to the History of Cryptography - 2 Hour of Sleep Facts about Cyphers, Enigma, Encription
7 months ago - 2:36:13

Jon King
Cryptanalysis - Boomerang Attack
14 years ago - 19:36

Cyber Technology
How Hackers Break Encryption | Cryptanalysis Attacks Made Simple
8 months ago - 3:55

AVLexis
What is the meaning of the word CRYPTANALYSIS?
5 years ago - 0:40

Cryogenicist Global Awards
AI Cracks Optical Encryption 🔐💡 | Deep Learning in Cryptanalysis #sciencefather #researchawards
6 months ago - 0:39

Jon King
Cryptanalysis - Slide Attack
14 years ago - 25:31
InfoSec Guardians
Mastering Cryptanalysis: Unlocking the Secrets of Cryptographic Systems -Domain 3 CISSP & CISM, CISA
2 years ago - 6:25
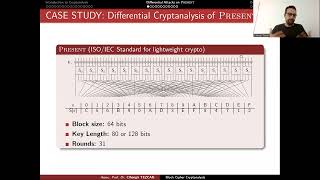
Cihangir Tezcan
Differential Cryptanalysis of PRESENT Block Cipher
3 years ago - 31:46

OpenSSL Conference
OpenSSL Conference 2025 - Peter Gutmann - Why Quantum Cryptanalysis is Bollocks
5 months ago - 33:59

Tharunika
AI Driven Cryptanalysis | breaking codes and strengthening security
6 months ago - 15:21

Zach Star
The Mathematics of Cryptography
7 years ago - 13:03

Becket U
How An Exiled Child Became the Father of Cryptography?! 🤯
11 months ago - 0:52

FreeAcademy
What is Cryptanalysis? #triviaquestions #cybersecurity #ethicalhack #computersoftware #chatgpt
1 year ago - 0:24

IACR
A Geometric Approach to Linear Cryptanalysis
4 years ago - 29:31

SUKANYA BASU
Different Cryptanalysis Attacks
4 years ago - 0:05

Jordan Brown
Cracking the Code: Police Investigate Mysterious Cipher | #Mystery #PuzzleSolving #Clues
2 years ago - 0:42

Husmerk TECH
Cryptography #Tutorial Source | #blockchaindevelopment #free #tutorial | #shorts | #husmerktech
1 year ago - 0:17

Vocabulary Vault
Understanding Cryptanalysis: Unlocking the Secrets of Encrypted Language
2 years ago - 2:51

IACR
Differential Cryptanalysis - talk 1/2 (FSE 2025)
7 months ago - 20:49
Koncept Recall
Bruteforce Cryptanalysis of Caesar Cipher | Cryptography | Chapter 2 | Lecture 16
1 year ago - 5:02

Lionel Faleiro
Practical - Study of Cryptanalysis Tools
10 years ago - 28:13

Padho Engineering
Explain the term Cryptanalysis| NIS| Important Concept| Cryptography| Security| Padho Engineering
1 year ago - 4:45

MY SWAYAM
Cryptography and Network Security Week 1 | NPTEL ANSWERS 2026 #nptel2026 #myswayam #nptel
3 months ago - 2:53

Nolan Hedglin
Decoding Cryptography Lecture 1: Early Encryption (Pt 1)
5 years ago - 9:43

Noah Aydin
Al-Kindi's Cryptanalysis: The Origin of the Frequency Analysis
4 years ago - 4:50

MY SWAYAM
Cryptography and Network Security Week 3 | NPTEL ANSWERS 2026 #nptel2026 #myswayam #nptel
3 months ago - 2:55

Maria Eichlseder
Cryptanalysis - L8 Linear Cryptanalysis
Streamed 5 years ago - 2:00:52

Cihangir Tezcan
Impossible Differential Cryptanalysis of HIGHT
2 years ago - 29:03

Shreya's E-Learning
Cryptography and Network Security:#10 Cryptanalysis for Additive Ciphers
5 years ago - 7:35

Real History
The History Of Codebreakers And Cryptography During WW2
6mo ago - 23:47
Fiona Lau
Acoustic Cryptanalysis
4y ago - 10:04

OpenSSL Conference
OpenSSL Conference 2025 - Peter Gutmann - Why Quantum Cryptanalysis is Bollocks
5mo ago - 33:59

Cihangir Tezcan
Cryptanalysis 9.2: Collisions for AES Hashing Modes
4y ago - 16:02

Anjunabeats
Who.Is - Cryptanalysis (Original Mix)
14y ago - 3:34

Yohan Jhaveri
RSA Key Extraction via Low-Bandwidth Acoustic Cryptanalysis
5y ago - 9:57

TechTeach
Understanding Cryptanalysis and Its Goal
10 months ago - 0:30

Ritika xRay Pixy
Role of Cryptography in Information Security ~xRay Pixy
5 years ago - 9:45

MY SWAYAM
Cryptography and Network Security Week 12 | NPTEL ANSWERS 2026 #nptel2026 #myswayam #nptel
1 month ago - 3:54

TechTeach
Caesar cipher Cryptanalysis using frequency analysis
10 months ago - 10:26

Mohammad Ali Humayun
L5: Differential Cryptanalysis for Symmetric Block Ciphers
2 months ago - 28:30

TeachCyber
Foundations of Cybersecurity: Symmetric Key in Response to Cryptanalysis Video Lecture
1 year ago - 14:20

MY SWAYAM
Cryptography and Network Security Week 9 | NPTEL ANSWERS 2026 #nptel2026 #myswayam #nptel
1 month ago - 4:08

MY SWAYAM
Cryptography and Network Security Week 11 | NPTEL ANSWERS 2026 #nptel2026 #myswayam #nptel
1 month ago - 4:14

Learn With Surendra
“Cryptanalysis Made Super Easy | All Attacks Explained with Examples | University Exams Special”
5 months ago - 17:18

MHZ Studio
4 - Introducing Cryptanalysis
3 years ago - 5:02

MY SWAYAM
Cryptography and Network Security Week 7 | NPTEL ANSWERS 2026 #nptel2026 #myswayam #nptel
2 months ago - 3:05

Learn.in.1Min
Vigenere cipher and it’s cryptanalysis
3y ago - 3:48

Gate Smashers
Lec-88: Cryptography in computer network in Hindi | Cryptography in Information Security
7y ago - 7:39

IACR
Symmetric Cryptanalysis 2 (Crypto 2024)
1y ago - 1:33:43

Intellipaat
What is Cryptography | Cryptography Explained | Cryptography Basics | Intellipaat
4y ago - 2:18

Tactical Warfare Experts
What Is The Role Of Letter Frequency In Cryptanalysis? - Tactical Warfare Experts
1y ago - 2:53

CSE Adil
Monoalphabetic Cipher | Monoalphabetic Cipher Security | Language Redundancy and Cryptanalysis
2y ago - 7:53

Free College
Introduction to cryptography, Caesar Cipher, Cryptanalysis
2y ago - 22:18

MY SWAYAM
Cryptography and Network Security Week 8 | NPTEL ANSWERS 2026 #nptel2026 #myswayam #nptel
2 months ago - 3:06

IACR
session-28: Cryptanalysis of authenticated encryption schemes
Streamed 4 years ago - 53:07

Barry Burd
Breaking Code in the Quantum Era: An Introduction to Quantum Cryptanalysis
1 year ago - 1:19:33

Elie Bursztein
Deep-Cryptanalysis - Fashion or Revolution?
4 years ago - 36:34

Anh Tuấn Đinh
AI in Automated Cryptanalysis and Key Recovery
1 year ago - 10:09

TechKnow
15 Playfair Cipher Cryptanalysis
5 years ago - 6:43

Jon King
Layerone 2013 - Differential Cryptanalysis for Dummies - Jon King
12 years ago - 38:49

S-TechMatrix
Vigenere Cipher Explained | Strengths, Weaknesses & Cryptanalysis
2 months ago - 20:40

Roger Hallman
EveGAN: Using Generative Deep Learning for Cryptanalysis - ACM CCS 2022 Poster Session
3 years ago - 2:10

rathod_sir
NIS-3.1 Cryptography (Plain Text, Cipher Text, Cryptology, Cryptanalysis, Encryption, Decryption)
5 years ago - 35:56